Cyberbit Range simulation-based exercises are aligned with NICE Work Roles and KSAs, suitable for practitioners, managers and students.
OT attack simulation scenarios are available for OT security training.
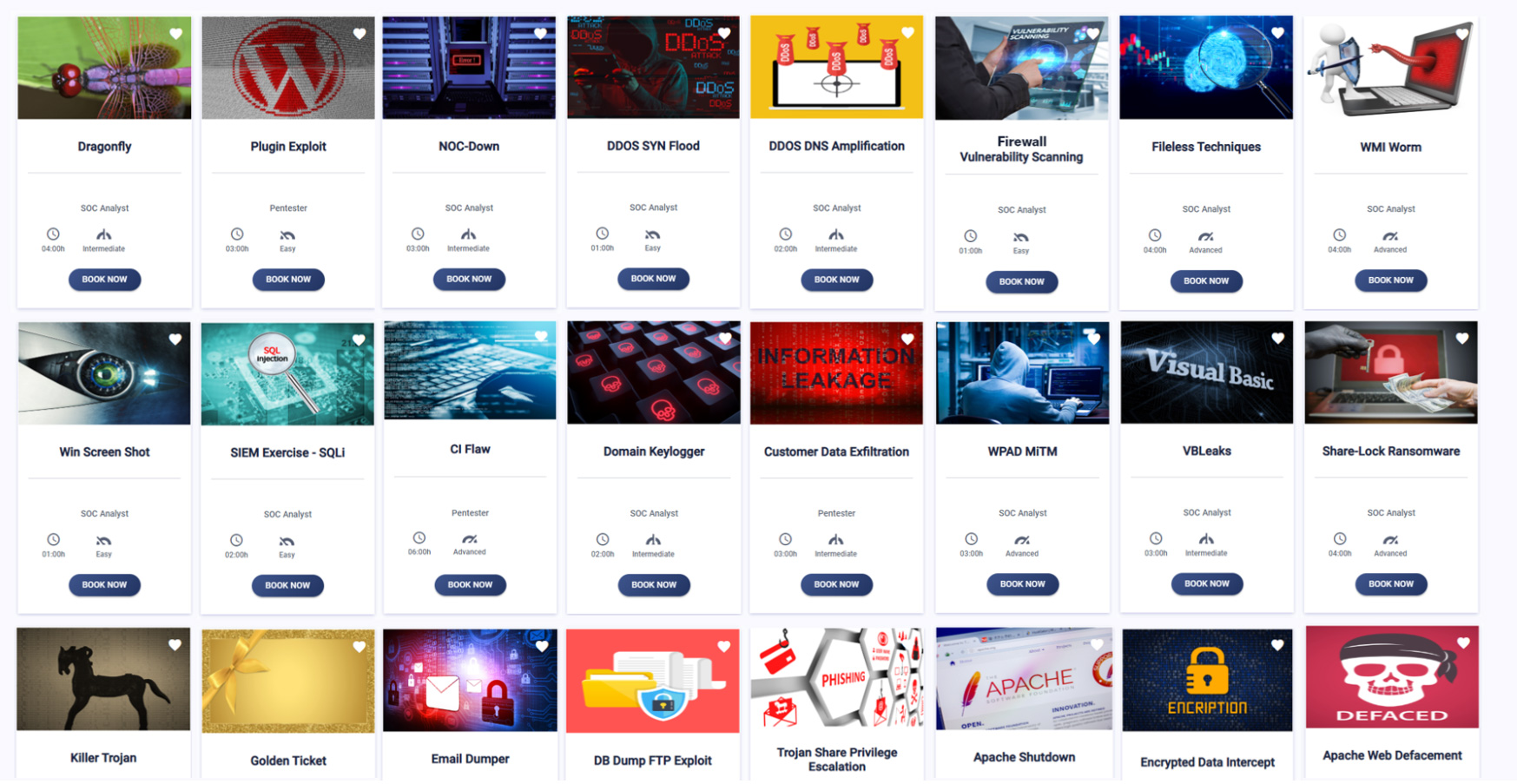
A Comprehensive Catalog of Simulation Exercises
Train for Real
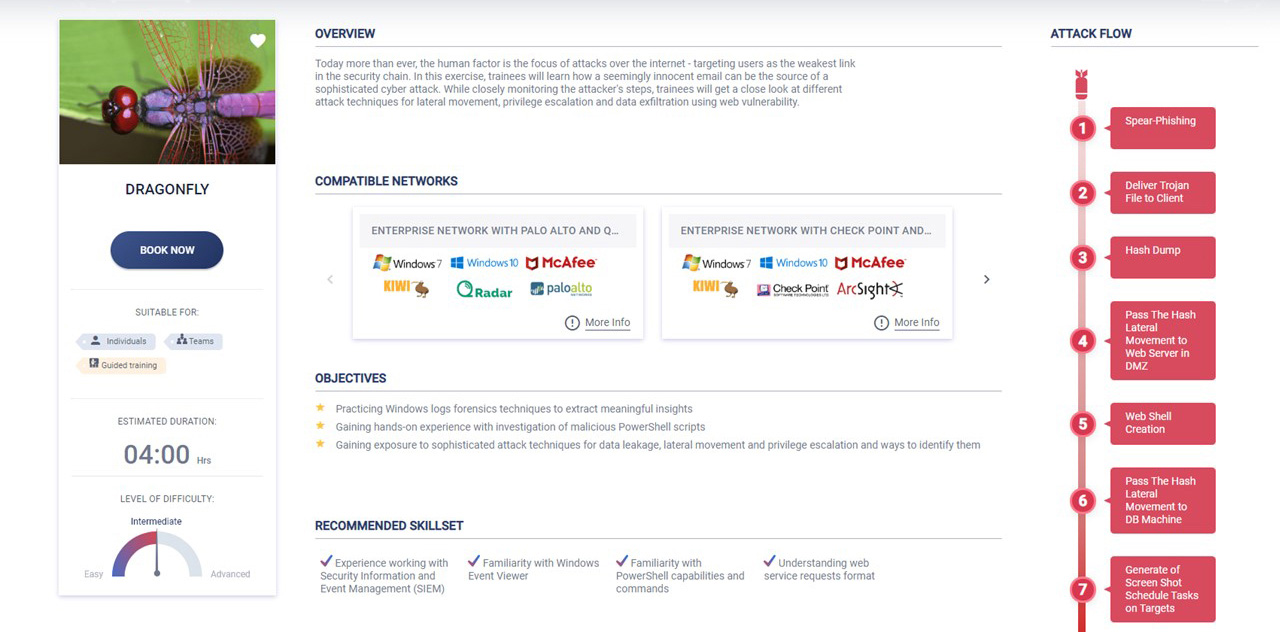
Cyberbit Range trainees confront a simulated attacker, executing an end-to-end cyberattack, from infection, through persistence, to data exfiltration. Our exercises are built for cyber experts, novices, and hopefuls by cyber experts, who reverse-engineer real-world malware to ensure the most realistic experience possible for your team.